“There is no backup system to the grid.”
– Gretchen Bakke from her book,
The Grid: The Fraying Wires Between Americans and Our Energy Future
On March 15, 2018, the US government made a chilling announcement. Russian hackers have been successfully infiltrating the US electric grid over the last year, maybe longer. While rumors have been swirling for some time, this news confirms two things. First, the cyberattacks originated from Russia. Second, the infiltration goes much deeper than the utilities’ email and file servers. Hackers had breached the industrial control systems – the computers that directly control the transformers, power plants, and substations.
The grid is more vulnerable to cyberattacks than most people want to acknowledge
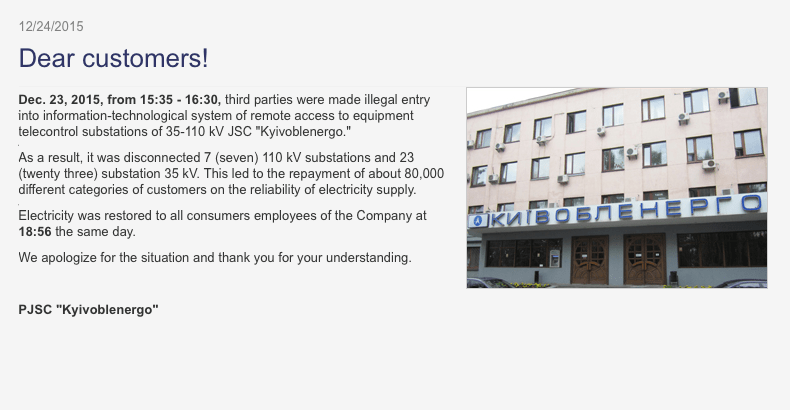
This isn’t the first time a grid has been hacked. Just two days before Christmas 2015, hackers not only infiltrated the Ukrainian electric grid, they shut it down. A quarter-million people suffered a complete electrical blackout for almost six hours. While the power was restored within hours, the damage lasted for weeks. The hackers didn’t just disable the circuit breakers and transformers, they overwrote the firmware on the computers that control those devices. No more remote monitoring. No more automated control. In tech-lingo, the hackers “bricked” the industrial control computers. The damage was so complete, it took weeks to replace and reprogram the computers. During that time, the grid had to be manually controlled. If the Ukraine grid had been an airplane, it would have been like flying at night with no autopilot, no radar, and no radio.
Most experts agree that the Ukraine grid attack was a dress rehearsal for a bigger plan. For instance, the Ukrainian industrial control computers are the same kind used by most utilities in the US. On the other hand, the Ukrainian grid hardware had manual overrides, but much of the US grid lacks this feature. To put it bluntly, the cyberattacks in Ukraine would likely work just as well in the US. And the lack of manual backups in the US could extend blackouts for days or longer.
Hacked computers can not only disable equipment, they can destroy it

Cyberattacks are not just about cyberspace – their damage can extend into the physical world as well. In 2009, a cyber weapon called Stuxnet is credited with sabotaging Iran’s primary uranium processing plant at Natanz. Despite the facility being underground and isolated from any computer networks, Stuxnet managed to destroy 30% of the centrifuges. Stuxnet spread across Iran by hopping silently between networked computers. It ultimately found its way to the Natanz facility.
From there, it leaped across disconnected networks by invisibly piggybacking on the USB memory sticks that were used to update the centrifuges’ industrial control computers. Stuxnet then took over. By making small but jarring changes in speed, the cyber weapon slowly burned out the motors and gears of the centrifuges. Over a few months, it rendered nearly 1,000 of them inoperable.
GET MONTHLY NEWS & ANALYSIS
Unsubscribe anytime. We will never sell your email or spam you.
Nine substations can take out the entire US grid
In 2015, a report was leaked from the agency that oversees the US grid. It said, in part:
“Destroy nine interconnection substations and a transformer manufacturer and the entire United States grid would be down for at least 18 months, probably longer.”
Out of the 55,000 substations across the US, there are nine whose loss can trigger a catastrophic domino effect and leave the US in the dark for years. It’s notable that the Ukraine attack took down 30 substations.
A multi-hour outage is annoying but very survivable. However, as an outage extends into a week, grocery stores empty out, water spigots can dry up, and diesel fuel for backup generators starts to become scarce.
While it’s almost too terrifying to ask, what if those nine substations were really destroyed?
What if it took a year or more to build replacements? This was the question posed to James Woolsey, former director of the Central Intelligence Agency, during a Senate hearing on grid vulnerability to an electromagnetic pulse (EMP) attack. While an EMP attack and cyberattack are not the same things, they both have the potential to shut down large portions of the US grid. Mr. Woolsey’s answer is terrifying,
“There are essentially two estimates on how many people would die from hunger, from starvation, from lack of water, and from social disruption. One estimate is that within a year or so, two-thirds of the United States population would die. The other estimate is that within a year or so, 90% of the U.S. population would die. We’re talking about total devastation. We’re not talking about just a regular catastrophe.”
It’s important to note that experts do not all agree that the grid is this vulnerable. Nor do they agree that an extended outage would be so dire. But the mere fact that it’s possible should be a wake-up call to citizens and utilities alike.
The Freeing Energy perspective
It’s easy to lose sleep over all this. But the fact is that a scenario like this remains unlikely. Any effective cyberattack on the grid requires incredible resources and years of patience. And that’s just to shut down a portion of the grid for a day or so. Writing code that can physically destroy equipment requires an entirely new level of resource and challenge. But as Home Depot, Equifax, and even the NSA have shown us, not to mention the Ukraine and Iran, even the most secure systems are vulnerable to determined hackers.
My next article talks about three ways we can reduce the risk and impact of cyberattacks on the grid.
Further reading
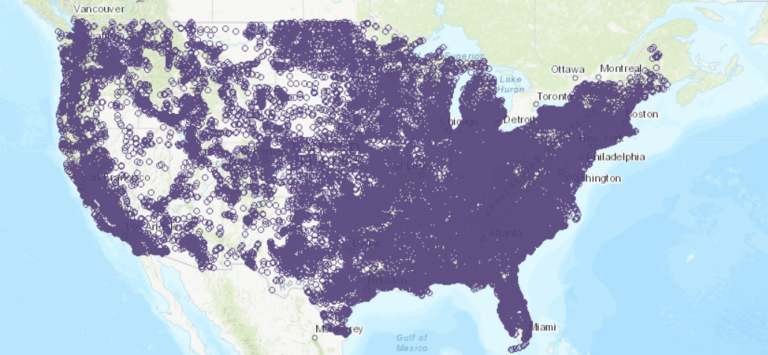
Check out the US Energy Information Administration’s interactive map for the location of all the critical energy infrastructure across the US.
 Ted Koppel’s book Lights Out: A Cyberattack, A Nation Unprepared, Surviving the Aftermath, is a frighteningly descriptive book about just how vulnerable the US power grid is to foreign attacks.
Ted Koppel’s book Lights Out: A Cyberattack, A Nation Unprepared, Surviving the Aftermath, is a frighteningly descriptive book about just how vulnerable the US power grid is to foreign attacks.